Is there a Deep web?
NO, I’m sorry to disappoint you, but it does not exist as you have been told. Urban legends have wrongly presented us with the Deep Web, like this:
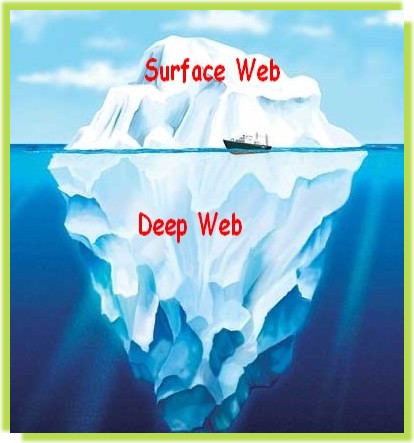
So why actually is it called Deep Web or dark web?
The “Deep Web” as I will continue to call it throughout this article to avoid confusion with other terms, actually represents the inverse of the previous image, and is better represented as follows:

You see, the information on the regular Internet that you access every day is stored in millions of servers of thousands and thousands of gigabytes each. Hosting of web pages, files, social networks, blogs, forums, multimedia, databases of companies, etc. Therefore the internet is huge, with millions of databases hosting, billions of files ready to be accessed.
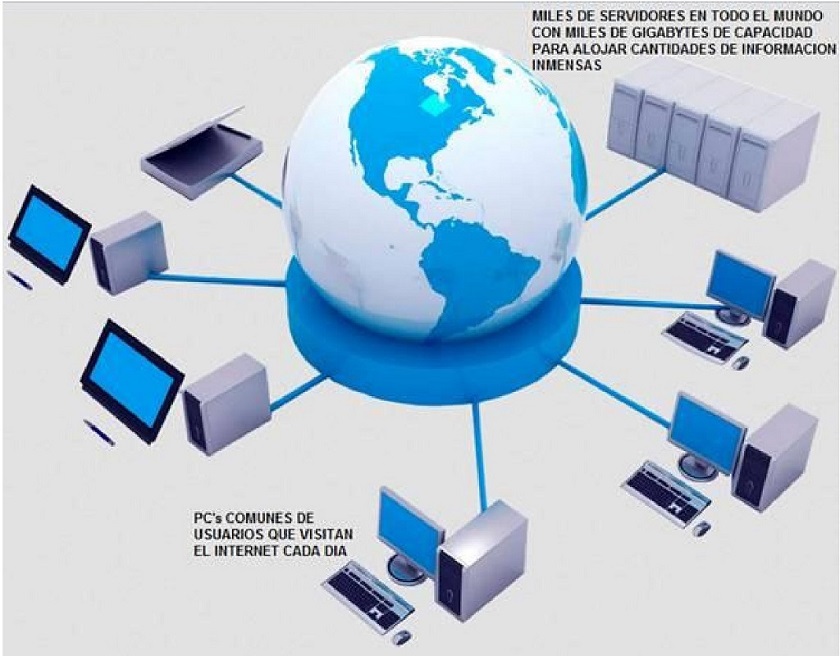
Deep Web, on the other hand, is based on simple sites of very basic programming, created and hosted on common PCs, of average processing capacity and data storage, such as the PC you are using to navigate at this moment. , except for a few and few exceptions of expert users who mount on the Deep Web servers for hosting sites, files and email, charging some amount of money.
And for that reason the anonymous networks have little storage capacity, almost no servers exist, and of those that exist, few keep databases of small size, where there are files, anonymous mail accounts, etc., without forgetting that all this set of anonymous networks poorly named “Deep Web” is still dependent on you have a connection to the ordinary Internet, so in turn, the Deep Web happens to form a small portion within the regular Internet, and not a large part below her as you have been led to believe.
Who uses the Deep Web?
There are two main classes of users that enter the “Deep Web”. The first is the average user, curious, low level, inexperienced in the use of tools for anonymous browsing, and who enters using free software called Tor, which you can download from here: https://www.torproject.org/projects/torbrowser.html.en

Thanks to this class of users are that they began to mythify the concepts of the Deep Web, they began to invent the legends of the famous “levels” of the Deep Web and invented the legend of the deepest level called “Marianas Web”, alluding to the Mariana Trench, which is the deepest known oceanic trench and the deepest place in the Earth’s crust.
Here before continuing we must point out something: The Deep Web is not Tor nor are the pages ‘.onion’. Tor is just one of the many means to anonymize your connection, and NO, Tor is not used by hackers, governments, aliens, Satanist sects, Illuminati, or anything like that.
Well, already explained this, the second class of users, encompasses a large number of people in many specialties.
Some examples are:
1. Journalists and war correspondents who use the different anonymous connections to send their news centers filtered photos of war or information that the government does not want people to know and the news make it public.
2.People who publish books, notes, writings or documentation considered in their country as an anarchist, and that due to the government regime in which they live, they can go to jail.
3. People who want to communicate with the world simply, use web browsers, have an email account, and other services just like you do, but in your country this is illegal, and the government has installed in the service providers of Internet (ISP), restrictive firewalls that prevent people from browsing freely through the internet and can only access sites previously authorized by those governments (a clear example are Venezuela, North Korea, China, Cuba, etc …).
4. Governments and militia, using their own anonymization and encryption channels, exchange sensitive information between two or more points.
5. Hackers, who use their own means of anonymity and security in the same way, exchange information of a nature that we will not discuss for now.
Then there are the famous levels of the Deep Web, The “Marianas Web”?
No. They do not exist. I explain:
I’m sorry to disappoint you. The “famous levels” The “Marianas Web” does not exist, there are no sites that you can only access by solving science fiction novel quantum algorithms, or sites hosted on super servers based on DNA, or web hosting with classified information UFO, nor who killed JFK, nor the truth about the twin towers, nor the plans of the Middle East to invade North America, there are no plans to create a spaceship or a bomb.
Think about it a little, what do these users who supposedly have entered call these levels?
On the other hand, we can mention that yes there are two types of sites in any anonymous network:
The first type is places you will never be able to enter. And you will not be able to enter, not because they are “levels” nor are they protected by hackers, governments or Illuminati aliens. You will simply never enter because their URL’s are not published in any list that you can find browsing through looking for how to enter Deep Web.
Also, Read:- Does “Marianas Web” Really Exist | The level 4 of deep web
Most people who use Deep Web in a professional manner keep their media in strict secrecy to exchange information in a secure manner, in addition to protecting access to their sites through accounts, as simply and as you protect your email account or Facebook so that nobody else enters.
The second type of sites is made up of all the URL’s and accesses that have become public domain, that is, you enter Google and typed: Deep Web addresses, and you get an immense list of sub-lists that contain links to pages, of which most are running under Tor (.onion) which is the most basic method and the favorite of beginners who enter the “Deep web”, are pages made by users ranging from the average to the average level in the use of web programming and assembly of a very basic webserver to create your ‘.onion’ sites.
This type of sites is divided into genres, which have helped to mythologize the Deep Web and create an aura of mysticism and fear to enter, fed by ignorant people who publish common and current information in social networks and forums, affirming that it came down from the supposed Deep Web. Normally these users have the clumsy idea that the Deep Web is Tor and surfing this network is to enter sites ‘.onion’, which you and any ordinary person can enter without a major problem and later I will explain how to enter by yourself.
Among these genres of sites we find:
- Gore sites
- Sites for supposedly buying drugs
- Sites with supposedly classified information
- Sites with pedophile content (these abound, you must be careful where you click)
- Alleged satanic sects
- Alleged sites of the Illuminati
- Forums very basic and poor design, 4chan style (like chan onion), where anyone can post anything and pass it off as true.
In these places, you will find alleged assassins, alleged hackers offering their services, fictitious sects, people who change your identity, organ trafficking, drug sales, alleged kidnappers, people selling bitcoins (of which we will talk later), children asking how to hack mail accounts and Facebook, among others.
At this point, it should be clarified that to be a hacker it takes many years dedicated to programming and specialization in networks, and learn several programming and encryption languages. You will not learn to hack with a book that you download from the internet that is called “Learn to hack”, nor will you hack an account of an acquaintance just by entering a website that says “I teach you how to hack accounts”.
It is also worth mentioning that not everything is to waste your time in this network if you are a new user because there are also sites for the exchange of books, images, very interesting blogs, specialized discussion forums, social networks like Facebook and Twitter, host of email, chats, etc …
Is it illegal to enter the Deep Web?
No. It is not illegal.
It’s okay to enter Deep Web to take a look, and being honest with you, you will be able to really do little browsing through the anonymous networks, because you do not belong to a group of advanced users (journalists, government, minority classes of a country socialist, activists, hackers, etc.) that use it properly, so that your contact and interaction with other people will be basically scarce and the information that you can find as a non-member of this group will be found in the same way circulating on the regular internet.
On the other hand, they have arrested people for misusing Deep Web.
but before browsing onion websites or .onion links make sure you have a safeguard or a firewall from anyone who can hack your system or attack your personal privacy. consider any VPN, but make sure that you are completely protected, anonymous, and on an AES 256-bit encrypted network. I recommend you this, click here for free VPN
The most famous case is that of Eric Eoin Marques, a 28-year-old Irishman classified by the FBI as the “greatest facilitator of child pornography on the internet”, whose story you can read here: Click Here for the full story.
It should be noted that Deep Web traffic was drastically reduced after the FBI entered to arrest this individual and others, and many average users who hosted Deep Web sites on their computers about gore, conventional pornography, pdf books, they passed themselves off as sects or Illuminati, among others, closed their sites out of fear. Clara shows the ignorance of these people who were not prepared to really face “the myth of what it means to move on the Deep Web”, because they do not have well-encrypted connections to their sites or offer anything more than low-quality entertainment such as aforementioned.
Does the FBI, the CIA, the aliens, the Illuminati, Green Peace, and the Pope watch over me every time I enter the Deep Web?
No, Nobody watches you when you enter the Deep Web. No one is monitoring your internet connection if you have not been doing something wrong for several years. To get caught doing something wrong, you must first do it, and you must take several false steps and make typical mistakes as the only people the FBI has arrested within the Deep Web: Pedophiles.
And for this they used many methods, mainly identity theft by agents to pose as potential clients of pedophile sites, pretending to be children, creating fake pornography servers waiting for someone to search for illegal content, and using a software called ‘ Sweetie ‘from which you can learn more by watching this video:
Can I use a cell phone or tablet to access Deep Web?
NOT as such. You can not access the different anonymous networks from a conventional cell phone unless it is a high-end Smartphone and you have installed a version of Linux compatible with such anonymous software (such as the Ubuntu Phones).
However, Tor is available for smartphones and tablets of average range to browse anonymously on the Internet. It’s nothing spectacular, just apply an anonymous proxy to your navigation, now you know it, so they do not talk to you.
But there is an update for the accessing deep web on the smartphone here you can find all the information about access deep web on smartphone
Is it safe for my PC to enter the Deep Web?
Yes and no. I explain:
It is not plagued by hackers stalking who enters to harm him. It is not full of viruses in every link you visit (in fact the spread of viruses through the Deep Web is merely scarce and you may download an infected file that is hosted on an anonymized PC that has viruses in the operating system, possibly Windows).
But beware, there are pirate FBI servers, posing as pedophilia sites to catch whoever connects to these places, and when you connect, if you are a rookie user who got off Tor and entered Windows, then you don’t have security minimum and can connect to your PC, scan its content for illegal material, access your accounts opened at the moment or saved in the browser, such as mail, Facebook, Twitter, Bank, etc.
There are also people from the FBI posing as people who offer you to send you illegal content for free if you give them your email address, anonymous or not, and by contacting them they can track you and do everything mentioned on your PC.
On the other hand, those who claim to sell drugs, organs, be murderers, sectarians, change your identity, open accounts, sell someone’s information, teach you hacking and offer to hack, etc., 100% of these cases are people who simply want to call the Attention. So you do not have to worry about them. But I repeat again, waters with pedophilia, which besides being a low and vulgar entertainment for ordinary people, is highly risky and they will catch you sooner or later.
So, How to Access The Dark Web Safely
As I already told you above the most crucial step before entering deep web/dark web, make sure a strong VPN software is running in the background. You can consider this Free VPN to safeguard you PC and you from hackers and deep web peoples
I will emphasize at this point that if you are going to use Windows, you should be careful if you are going to deliberately enter illegal content, either out of curiosity or by accident, any link you open can say that it is a Slenderman blog and actually is plagued by child pornography, or even if what you want to see is something illegal on purpose and you get the address of a website, that site could be from a fake server mounted by the FBI waiting for you to enter to scan your PC for content illegal and intervene. This is real if it happens, and yes they have done it as in the cases of pedophilia mentioned above. Later I will explain how to access the Tor network completely securely.
Also Read:- How to Access The Dark Web Safely
Well, having said that, to enter I will mention a bit of theory that you should know before launching yourself into the adventure, and then I will give you the links so you can learn to enter and download the necessary information.
In order of importance, the first and most infamous anonymous network of the Deep Web is Tor https://www.torproject.org/ which really is not a network, it is a proxy software that hides your location, IP address and addresses information physics of your computer, with this software installed in your web browser you can enter ‘.onion’ sites or surf the Internet regularly anonymously, but be careful, sites like Google, Facebook, and others, collect information from your navigation, and What accounts do you enter and from where so it does not matter much if you surf the Internet regularly anonymously as the same servers are responsible for collecting what you do.
The complete software, called Vidalia, also gives you the possibility to use your PC as a host to host your own anonymous website by adding a ‘.onion ‘at the end of your user id for that to be your site.

The second most important is the i2p network with which you can browse, chat and exchange files anonymously through the i2p protocol, similar to the p2p that Ares uses for example (yes, the program is so useful that you download the free music from the Internet).
The i2P project was created for those who tried to create a free, anonymous and non-reprehensible society. Its objective is to establish a secure and anonymous network of low latency, which is distributed completely, autonomously, scalable, flexible and dynamic. I will not delve much into this network since it needs users of medium to a higher level, and if you are a user of this type then I have nothing more to talk about the i2p, because you know what it is and for what.

The third and the oldest of these is the Freenet recommended for advanced users, always in beta phase continuously improving themselves thanks to its community of programmers. It is the network most used by the groups of people we mentioned earlier to communicate safely and exchange files anonymously without fear of being censored.
A place where you will find many interesting sites especially in programming, news, political and social movements, books in several languages, music, movies, and much more. I highly recommend this network if you really want to get involved in the Deep Web theme. The operation is based on the P2P protocol, in which users contribute to the network with bandwidth and a part of their hard drive to store files and have two options: you can connect only with friends and other trusted users, or you can choose to participate with the entire network.
The communications of the Freenet nodes are encrypted and routed through other nodes, so that it is extremely difficult to determine who is requesting the information and what is its content, unlike Tor that only encrypts the origin of the data, but does not protect content. Freenet requires for its operation to have the Java platform installed. Your assistant does practically all the work at the time of installation, the use within it will depend on you.

Then How to enter the Deep Web safely?
I will explain how to enter the “Deep Web” using Tor because this network is the easiest to navigate and the most basic for novice users. It will be up to you to learn how to use the i2p and the Freenet that is more advanced (I recommend the Freenet if you want a complete and rich experience on the Deep Web).
If you still insist on using Windows to navigate, what else can I tell you?
To navigate from Windows you don’t have to do more than download this little software of just a few megabytes https://www.torproject.org/index.html.en
Once downloaded, install it in the folder of your choice, for example, the desktop, and you will see something like this:
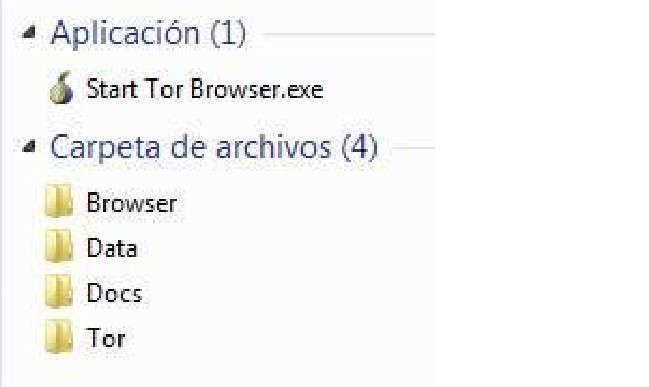
Activate your firewall and configure your internet access as a Public Network, with all security options enabled, preferably close any another browser and download program, chat, etc., that uses the internet, and double click on ‘Start Tor Browser’ and start browsing, although I repeat, it will be of little use to you, because Windows as such is a huge hole of security in the world (joke for computer scientists). To exit simply close the Tor browser and go.
Isn’t it true science? However, social networks and forums are full of “Deep Web experts” who spend sharing URLs of gore sites, pornography, and satanic books, talking about levels and all that nonsense. Now you can include yourself among them.
I leave you a list of web addresses (URL’s) to start safe and smooth navigation. Where you jump from these sites is entirely your responsibility:
The famous Hidden Wiki, although there are many, not a Wikipedia of the Deep Web, it is only a list of addresses and the page has the format of Wikipedia, so it became famous: http://zqktlwi4fecvo6ri.onion/wiki/index.php /Main_Page
OnionDir, another list of active addresses: http://dirnxxdraygbifgc.onion/
Another Hidden Wiki Onion Links, the same: http://jh32yv5zgayyyts3.onion/
Tor links, more of the same: http://torlinkbgs6aabns.onion/
Onion URL repository, the same again: http://32rfckwuorlf4dlv.onion/
WikiLeaks, the infamous page that exposed the secrets of the United States: http://zbnnr7qzaxlk5tms .onion /
Onion web file hosting, to upload files to the Deep Web: http://3fnhfsfc2bpzdste.onion/
Torbook, A Tor’s social network, with a format similar to Facebook: http://torbookdjwhjnju4.onion/
Mailtor, you can make your anonymous email account: http://mailtoralnhyol5v.onion
Tor mailbox, another mail service on the Deep Web: http://torbox3uiot6wchz.onion/
Deepweb Radio, an anonymous radio station: http://76qugh5bey5gum7l.onion/
In case you want to laugh for a while reading posts from people who have no idea what it says:
Cebolla chan, the 4chan in Spanish of the Deep Web and the paradise of people who want to call attention, mandatory entry if you want to feel like an “expert on the Deep Web”: http://s6cco2jylmxqcdeh.onion/
Thorlauta, another 4chan type site, sometimes someone posts something interesting (in English): http://zqiirytam276uogb.onion/
Anonymous BBS (Bulletin Board System), with quite paranoid people: http://qm3monarchzifkwa.onion/
Illuminati, one of many supposed Illuminati sites, nothing spectacular to see, you can even register and donate Bitcoins: http://6r3pg2kyrn5e7jjd.onion/ Example of a page on the Deep Web:

This is the first part of what is the deep web. You’ll get the second part here next week so stay tuned to know everything about deep web





![[Top 9] Chat Forums on Deep Web | Deep Web Chat Rooms | Enter At Your own Risk Top 9 Chat Forums on Deep Web, The Lolita City, onion deep web, dark web lolita, lolita city,](https://www.gadgetgyani.com/wp-content/uploads/2018/03/deep-web-CHAT-FORUMS.jpg)













